
The National Institute of Standards and Technology (NIST) is one of the standard-bearers in global cybersecurity. The U.S.-based institute’s cybersecurity framework helps organizations of all sizes understand, manage, and... Read more »
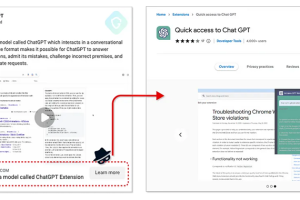
A fake ChatGPT-branded Chrome browser extension has been found to come with capabilities to hijack Facebook accounts and create rogue admin accounts, highlighting one of the different methods cyber... Read more »
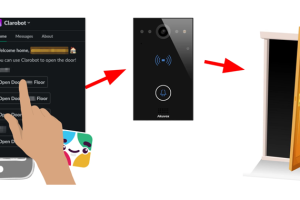
More than a dozen security flaws have been disclosed in E11, a smart intercom product made by Chinese company Akuvox. “The vulnerabilities could allow attackers to execute code remotely... Read more »
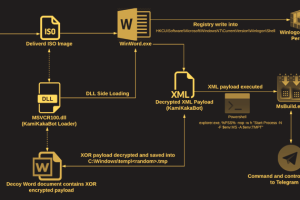
The Dark Pink advanced persistent threat (APT) actor has been linked to a fresh set of attacks targeting government and military entities in Southeast Asian countries with a malware called KamiKakaBot.... Read more »
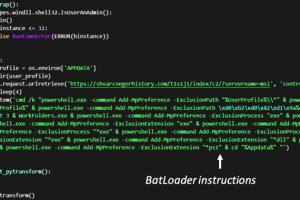
The malware downloader known as BATLOADER has been observed abusing Google Ads to deliver secondary payloads like Vidar Stealer and Ursnif. According to cybersecurity company eSentire, malicious ads are used to spoof... Read more »

A coordinated international law enforcement exercise has taken down the online infrastructure associated with a cross-platform remote access trojan (RAT) known as NetWire. Coinciding with the seizure of the... Read more »
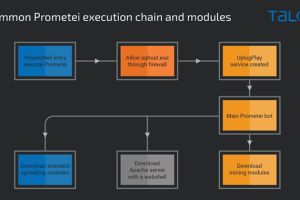
An updated version of a botnet malware called Prometei has infected more than 10,000 systems worldwide since November 2022. The infections are both geographically indiscriminate and opportunistic, with a majority of... Read more »

A suspecting China-linked hacking campaign has been observed targeting unpatched SonicWall Secure Mobile Access (SMA) 100 appliances to drop malware and establish long-term persistence. “The malware has functionality to steal user... Read more »

Multi-factor Authentication (MFA) has long ago become a standard security practice. With a wide consensus on its ability to fend off more than 99% percent of account takeover attacks,... Read more »
A new variant of the Android banking trojan named Xenomorph has surfaced in the wild, the latest findings from ThreatFabric reveal. Named “Xenomorph 3rd generation” by the Hadoken Security... Read more »

