
Cloud Security Posture Management (CSPM) and SaaS Security Posture Management (SSPM) are frequently confused. The similarity of the acronyms notwithstanding, both security solutions focus on securing data in the cloud. In... Read more »
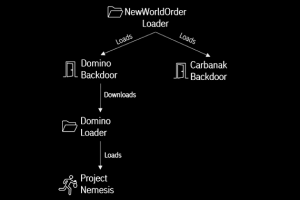
A new strain of malware developed by threat actors likely affiliated with the FIN7 cybercrime group has been put to use by the members of the now-defunct Conti ransomware... Read more »

The Deep, Dark Web – The Underground – is a haven for cybercriminals, teeming with tools and resources to launch attacks for financial gain, political motives, and other causes.... Read more »

A Chinese nation-state group targeted an unnamed Taiwanese media organization to deliver an open source red teaming tool known as Google Command and Control (GC2) amid broader abuse of... Read more »
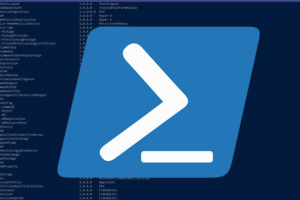
Threat actors associated with the Vice Society ransomware gang have been observed using a bespoke PowerShell-based tool to fly under the radar and automate the process of exfiltrating data... Read more »

A novel credential-stealing malware called Zaraza bot is being offered for sale on Telegram while also using the popular messaging service as a command-and-control (C2). “Zaraza bot targets a large number of web browsers... Read more »

Google on Friday released out-of-band updates to resolve an actively exploited zero-day flaw in its Chrome web browser, making it the first such bug to be addressed since the... Read more »
The Russia-linked APT29 (aka Cozy Bear) threat actor has been attributed to an ongoing cyber espionage campaign targeting foreign ministries and diplomatic entities located in NATO member states, the European Union,... Read more »

Open source media player software provider Kodi has confirmed a data breach after threat actors stole the company’s MyBB forum database containing user data and private messages. What’s more,... Read more »

In today’s fast-paced and ever-changing digital landscape, businesses of all sizes face a myriad of cybersecurity threats. Putting in place the right people, technological tools and services, MSSPs are... Read more »

