
Government, aviation, education, and telecom sectors located in South and Southeast Asia have come under the radar of a new hacking group as part of a highly-targeted campaign that... Read more »
Poorly managed Microsoft SQL (MS SQL) servers are the target of a new campaign that’s designed to propagate a category of malware called CLR SqlShell that ultimately facilitates the deployment of... Read more »

A former employee of Ubiquiti has been sentenced to six years in jail after he pleaded guilty to posing as an anonymous hacker and a whistleblower in an attempt to extort... Read more »
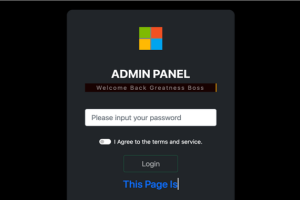
A new phishing-as-a-service (PhaaS or PaaS) platform named Greatness has been leveraged by cybercriminals to target business users of the Microsoft 365 cloud service since at least mid-2022, effectively lowering the... Read more »
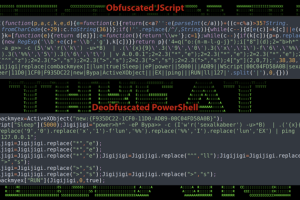
Cybersecurity researchers have discovered an ongoing phishing campaign that makes use of a unique attack chain to deliver the XWorm malware on targeted systems. Securonix, which is tracking the activity cluster... Read more »
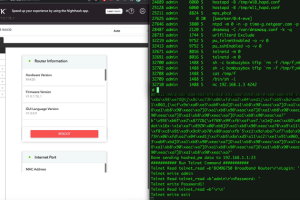
As many as five security flaws have been disclosed in Netgear RAX30 routers that could be chained to bypass authentication and achieve remote code execution. “Successful exploits could allow... Read more »

A previously undocumented and mostly undetected variant of a Linux backdoor called BPFDoor has been spotted in the wild, cybersecurity firm Deep Instinct said in a technical report published this week.... Read more »

In today’s interconnected world, where organisations regularly exchange sensitive information with customers, partners and employees, secure collaboration has become increasingly vital. However, collaboration can pose a security risk if... Read more »

U.S. cybersecurity and intelligence agencies have warned of attacks carried out by a threat actor known as the Bl00dy Ransomware Gang that attempt to exploit vulnerable PaperCut servers against the education... Read more »

A security vulnerability has been disclosed in the popular WordPress plugin Essential Addons for Elementor that could be potentially exploited to achieve elevated privileges on affected sites. The issue, tracked as... Read more »

