
A stealthy China-based group managed to establish a persistent foothold into critical infrastructure organizations in the U.S. and Guam without being detected, Microsoft and the “Five Eyes” nations said on Wednesday. The tech... Read more »

Google on Wednesday announced the 0.1 Beta version of GUAC (short for Graph for Understanding Artifact Composition) for organizations to secure their software supply chains. To that end, the search giant is making available the... Read more »

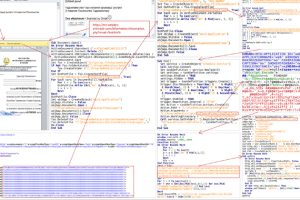
The Iranian threat actor known as Agrius is leveraging a new ransomware strain called Moneybird in its attacks targeting Israeli organizations. Agrius, also known as Pink Sandstorm (formerly Americium), has a track... Read more »

At least eight websites associated with shipping, logistics, and financial services companies in Israel were targeted as part of a watering hole attack. Tel Aviv-based cybersecurity company ClearSky attributed... Read more »

Google has removed a screen recording app named “iRecorder – Screen Recorder” from the Play Store after it was found to sneak in information stealing capabilities nearly a year... Read more »

If you’re involved in securing the applications your organization develops, there is no question that Static Application Security Testing (SAST) solutions are an important part of a comprehensive application... Read more »

An updated version of the commodity malware called Legion comes with expanded features to compromise SSH servers and Amazon Web Services (AWS) credentials associated with DynamoDB and CloudWatch. “This... Read more »

The North Korean advanced persistent threat (APT) group known as Kimsuky has been observed using a piece of custom malware called RandomQuery as part of a reconnaissance and information... Read more »
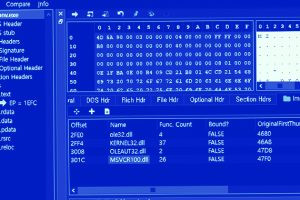
The infamous Lazarus Group actor has been targeting vulnerable versions of Microsoft Internet Information Services (IIS) servers as an initial breach route to deploy malware on targeted systems. The... Read more »
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of cyber attacks targeting state bodies in the country as part of an espionage campaign. The intrusion set, attributed to... Read more »

