
The term “attack surface management” (ASM) went from unknown to ubiquitous in the cybersecurity space over the past few years. Gartner and Forrester have both highlighted the importance of ASM recently, multiple... Read more »

Security vulnerabilities discovered in Honda’s e-commerce platform could have been exploited to gain unrestricted access to sensitive dealer information. “Broken/missing access controls made it possible to access all data... Read more »

A previously undetected cryptocurrency scam has leveraged a constellation of over 1,000 fraudulent websites to ensnare users into a bogus rewards scheme since at least January 2021. “This massive... Read more »

Fortinet has released patches to address a critical security flaw in its FortiGate firewalls that could be abused by a threat actor to achieve remote code execution. The vulnerability,... Read more »
Apple is introducing major updates to Safari Private Browsing, offering users better protections against third-party trackers as they browse the web. “Advanced tracking and fingerprinting protections go even further to... Read more »
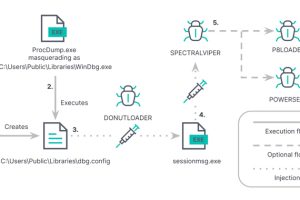
Vietnamese public companies have been targeted as part of an ongoing campaign that deploys a novel backdoor called SPECTRALVIPER. “SPECTRALVIPER is a heavily obfuscated, previously undisclosed, x64 backdoor that brings... Read more »

Progress Software, the company behind the MOVEit Transfer application, has released patches to address brand new SQL injection vulnerabilities affecting the file transfer solution that could enable the theft... Read more »
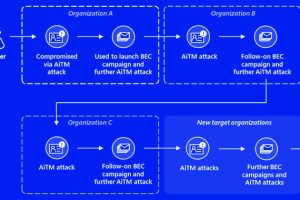
Banking and financial services organizations are the targets of a new multi-stage adversary-in-the-middle (AitM) phishing and business email compromise (BEC) attack, Microsoft has revealed. “The attack originated from a... Read more »

The threat actor known as Asylum Ambuscade has been observed straddling cybercrime and cyber espionage operations since at least early 2020. “It is a crimeware group that targets bank customers and... Read more »

The way we work has undergone a dramatic transformation in recent years. We now operate within digital ecosystems, where remote work and the reliance on a multitude of digital... Read more »

