
Microsoft on Wednesday took the lid off a “novel and distinct Russian threat actor,” which it said is linked to the General Staff Main Intelligence Directorate (GRU) and has... Read more »

The threat actors behind the LockBit ransomware-as-a-service (RaaS) scheme have extorted $91 million following hundreds of attacks against numerous U.S. organizations since 2020. That’s according to a joint bulletin published by the U.S.... Read more »

The Chinese state-sponsored group known as UNC3886 has been found to exploit a zero-day flaw in VMware ESXi hosts to backdoor Windows and Linux systems. The VMware Tools authentication bypass vulnerability,... Read more »
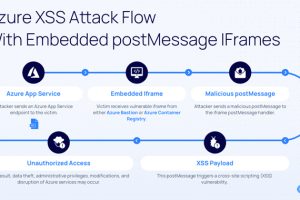
Two “dangerous” security vulnerabilities have been disclosed in Microsoft Azure Bastion and Azure Container Registry that could have been exploited to carry out cross-site scripting (XSS) attacks. “The vulnerabilities... Read more »

For the better part of the 90s and early aughts, the sysadmin handbook said, “Filter your incoming traffic, not everyone is nice out there” (later coined by Gandalf as... Read more »

A new Golang-based information stealer called Skuld has compromised Windows systems across Europe, Southeast Asia, and the U.S. “This new malware strain tries to steal sensitive information from its victims,” Trellix... Read more »

At least half of dozen GitHub accounts from fake researchers associated with a fraudulent cybersecurity company have been observed pushing malicious repositories on the code hosting service. All seven... Read more »
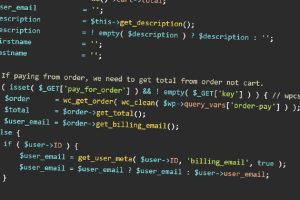
A security flaw has been uncovered in the WooCommerce Stripe Gateway WordPress plugin that could lead to the unauthorized disclosure of sensitive information. The flaw, tracked as CVE-2023-34000, impacts versions... Read more »

Microsoft has rolled out fixes for its Windows operating system and other software components to remediate major security shortcomings as part of Patch Tuesday updates for June 2023. Of the 73... Read more »
A novel multi-stage loader called DoubleFinger has been observed delivering a cryptocurrency stealer dubbed GreetingGhoul in what’s an advanced attack targeting users in Europe, the U.S., and Latin America. “DoubleFinger is... Read more »

