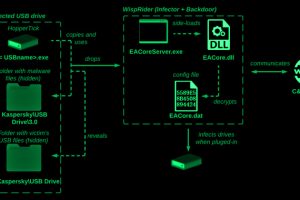
The Chinese cyber espionage actor known as Camaro Dragon has been observed leveraging a new strain of self-propagating malware that spreads through compromised USB drives. “While their primary focus has traditionally... Read more »

Millions of software repositories on GitHub are likely vulnerable to an attack called RepoJacking, a new study has revealed. This includes repositories from organizations such as Google, Lyft, and... Read more »

Losing sleep over Generative-AI apps? You’re not alone or wrong. According to the Astrix Security Research Group, mid size organizations already have, on average, 54 Generative-AI integrations to core... Read more »
Why Data Exfiltration Detection is Paramount? The world is witnessing an exponential rise in ransomware and data theft employed to extort companies. At the same time, the industry faces... Read more »

A critical security flaw has been disclosed in the WordPress “Abandoned Cart Lite for WooCommerce” plugin that’s installed on more than 30,000 websites. “This vulnerability makes it possible for an attacker... Read more »

Apple on Wednesday released a slew of updates for iOS, iPadOS, macOS, watchOS, and Safari browser to address a set of flaws it said were actively exploited in the wild. This... Read more »

The North Korean threat actor known as ScarCruft has been observed using an information-stealing malware with previous undocumented wiretapping features as well as a backdoor developed using Golang that... Read more »

More details have emerged about the spyware implant that’s delivered to iOS devices as part of a campaign called Operation Triangulation. Kaspersky, which discovered the operation after becoming one of the... Read more »
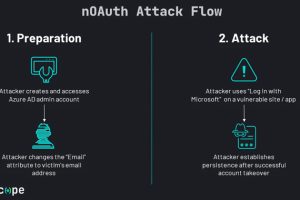
A security shortcoming in Microsoft Azure Active Directory (AD) Open Authorization (OAuth) process could have been exploited to achieve full account takeover, researchers said. California-based identity and access management... Read more »

When we do quarterly planning, my team categorizes our goals within four evergreen outcomes: Reduce the risk of information security incidents Increase trust in Vanta’s information security program Reduce the... Read more »

