
The threat actors behind the RomCom RAT have been suspected of phishing attacks targeting the upcoming NATO Summit in Vilnius as well as an identified organization supporting Ukraine abroad. The findings... Read more »
Businesses operating in the Latin American (LATAM) region are the target of a new Windows-based banking trojan called TOITOIN since May 2023. “This sophisticated campaign employs a trojan that follows a... Read more »

Two file management apps on the Google Play Store have been discovered to be spyware, putting the privacy and security of up to 1.5 million Android users at risk.... Read more »

Researchers have issued a warning about an emerging and advanced form of voice phishing (vishing) known as “Letscall.” This technique is currently targeting individuals in South Korea. The criminals... Read more »

Progress Software has announced the discovery and patching of a critical SQL injection vulnerability in MOVEit Transfer, popular software used for secure file transfer. In addition, Progress Software has... Read more »

Mastodon, a popular decentralized social network, has released a security update to fix critical vulnerabilities that could expose millions of users to potential attacks. Mastodon is known for its... Read more »

CISOs, security leaders, and SOC teams often struggle with limited visibility into all connections made to their company-owned assets and networks. They are hindered by a lack of open-source... Read more »

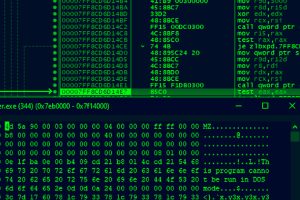
Ransomware attacks are a major problem for organizations everywhere, and the severity of this problem continues to intensify. Recently, Microsoft’s Incident Response team investigated the BlackByte 2.0 ransomware attacks... Read more »

Cybersecurity agencies have warned about the emergence of new variants of the TrueBot malware. This enhanced threat is now targeting companies in the U.S. and Canada with the intention... Read more »

JumpCloud, a provider of cloud-based identity and access management solutions, has swiftly reacted to an ongoing cybersecurity incident that impacted some of its clients. As part of its damage... Read more »

