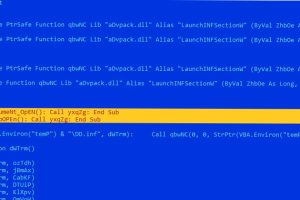
Microsoft Word documents exploiting known remote code execution flaws are being used as phishing lures to drop malware called LokiBot on compromised systems. “LokiBot, also known as Loki PWS, has been... Read more »
The Russia-linked threat actor known as Gamaredon has been observed conducting data exfiltration activities within an hour of the initial compromise. “As a vector of primary compromise, for the... Read more »

As security practices continue to evolve, one primary concern persists in the minds of security professionals—the risk of employees unintentionally or deliberately exposing vital information. Insider threats, whether originating... Read more »
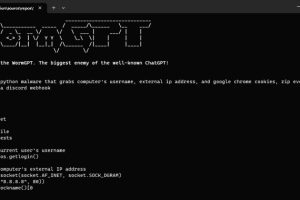
With generative artificial intelligence (AI) becoming all the rage these days, it’s perhaps not surprising that the technology has been repurposed by malicious actors to their own advantage, enabling... Read more »

Microsoft on Friday said a validation error in its source code allowed for Azure Active Directory (Azure AD) tokens to be forged by a malicious actor known as Storm-0558 using a... Read more »

Multiple security vulnerabilities have been discovered in various services, including Honeywell Experion distributed control system (DCS) and QuickBlox, that, if successfully exploited, could result in severe compromise of affected... Read more »
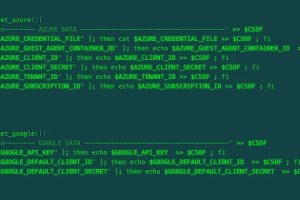
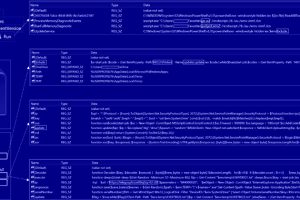
A malicious actor has been linked to a cloud credential stealing campaign in June 2023 that’s focused on Azure and Google Cloud Platform (GCP) services, marking the adversary’s expansion... Read more »

All-In-One Security (AIOS), a WordPress plugin installed on over one million sites, has issued a security update after a bug introduced in version 5.1.9 of the software caused users’... Read more »

Zimbra has warned of a critical zero-day security flaw in its email software that has come under active exploitation in the wild. “A security vulnerability in Zimbra Collaboration Suite... Read more »
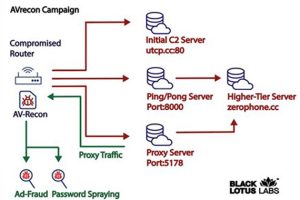
A new malware strain has been found covertly targeting small office/home office (SOHO) routers for more than two years, infiltrating over 70,000 devices and creating a botnet with 40,000... Read more »

