Cybersecurity researchers have uncovered a new cloud targeting, peer-to-peer (P2P) worm called P2PInfect that targets vulnerable Redis instances for follow-on exploitation. “P2PInfect exploits Redis servers running on both Linux and Windows... Read more »

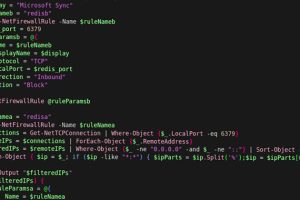
Microsoft on Wednesday announced that it’s expanding cloud logging capabilities to help organizations investigate cybersecurity incidents and gain more visibility after facing criticism in the wake of a recent espionage... Read more »

Adobe has released a fresh round of updates to address an incomplete fix for a recently disclosed ColdFusion flaw that has come under active exploitation in the wild. The... Read more »
U.S. cybersecurity and intelligence agencies have released a set of recommendations to address security concerns with 5G standalone network slicing and harden them against possible threats. “The threat landscape in 5G... Read more »

Attack surfaces are growing faster than security teams can keep up. To stay ahead, you need to know what’s exposed and where attackers are most likely to strike. With... Read more »

On April 5, 2023, the FBI and Dutch National Police announced the takedown of Genesis Market, one of the largest dark web marketplaces. The operation, dubbed “Operation Cookie Monster,” resulted... Read more »

The prolific China-linked nation-state actor known as APT41 has been linked to two previously undocumented strains of Android spyware called WyrmSpy and DragonEgg. “Known for its exploitation of web-facing... Read more »
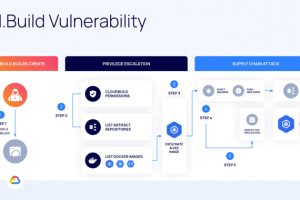
Cybersecurity researchers have uncovered a privilege escalation vulnerability in Google Cloud that could enable malicious actors tamper with application images and infect users, leading to supply chain attacks. The... Read more »

The U.S. government on Tuesday added two foreign commercial spyware vendors, Cytrox and Intellexa, to an economic blocklist for weaponizing cyber exploits to gain unauthorized access to devices and... Read more »

Citrix is alerting users of a critical security flaw in NetScaler Application Delivery Controller (ADC) and Gateway that it said is being actively exploited in the wild. Tracked as CVE-2023-3519 (CVSS score: 9.8),... Read more »

