
Hey ? there, cyber friends! Welcome to this week’s cybersecurity newsletter, where we aim to keep you informed and empowered in the ever-changing world of cyber threats. In today’s edition,... Read more »
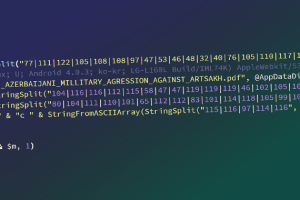
Entities in Armenia have come under a cyber attack using an updated version of a backdoor called OxtaRAT that allows remote access and desktop surveillance. “The tool capabilities include searching for... Read more »

A new variant of the notorious Mirai botnet has been found leveraging several security vulnerabilities to propagate itself to Linux and IoT devices. Observed during the second half of... Read more »

Cisco has rolled out security updates to address a critical flaw reported in the ClamAV open source antivirus engine that could lead to remote code execution on susceptible devices.... Read more »

The prolific SideWinder group has been attributed as the nation-state actor behind attempted attacks against 61 entities in Afghanistan, Bhutan, Myanmar, Nepal, and Sri Lanka between June and November 2021. Targets... Read more »

A popular npm package with more than 3.5 million weekly downloads has been found vulnerable to an account takeover attack. “The package can be taken over by recovering an... Read more »

Chinese-speaking individuals in Southeast and East Asia are the targets of a new rogue Google Ads campaign that delivers remote access trojans such as FatalRAT to compromised machines. The... Read more »
Security researchers have disclosed two new vulnerabilities affecting Schneider Electric Modicon programmable logic controllers (PLCs) that could allow for authentication bypass and remote code execution. The flaws, tracked as CVE-2022-45788 (CVSS... Read more »

Telecommunication service providers in the Middle East are being targeted by a previously undocumented threat actor as part of a suspected espionage-related campaign. Cybersecurity firms SentinelOne and QGroup are... Read more »
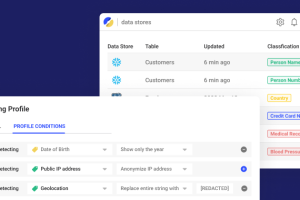
Security teams typically have great visibility over most areas, for example, the corporate network, endpoints, servers, and cloud infrastructure. They use this visibility to enforce the necessary security and... Read more »

