The BlackCat ransomware gang claims to have hacked the Casepoint legal technology platform used US agencies, including SEC and FBI. The cybersecurity researcher Dominic Alvieri first noticed that the... Read more »
Threat actors are actively exploiting a command injection flaw, tracked as CVE-2023-28771, in Zyxel firewalls to install malware. Threat actors are actively attempting to exploit a command injection vulnerability,... Read more »
Researchers discovered a suspected backdoor-like behavior within Gigabyte systems that exposes devices to compromise. Researchers from firmware security firm Eclypsium have discovered a suspected backdoor-like behavior within Gigabyte systems. The... Read more »
Recently disclosed zero-day flaw in Barracusa Email Security Gateway (ESG) appliances had been actively exploited by attackers since October 2022. The network security solutions provider Barracuda recently warned customers... Read more »
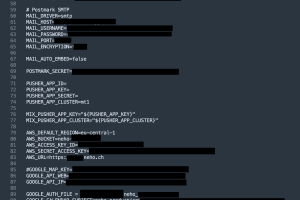
A misconfiguration of Swiss real estate agency Neho’s systems exposed sensitive credentials to the public. Neho, a Switzerland-based real estate agency, leaked credentials recently, potentially allowing threat actors to... Read more »
Apple fixed a vulnerability discovered by Microsoft researchers that lets attackers with root privileges bypass System Integrity Protection (SIP). Researchers from Microsoft discovered a vulnerability, tracked as CVE-2023-32369 and dubbed... Read more »
PyPI is going to enforce two-factor authentication (2FA) for all project maintainers by the end of this year over security concerns. Due to security concerns, PyPI will be mandating... Read more »
The database of the popular RaidForums hacking forum has been leaked on a new hacking forum, 478,000 members exposed. A database belonging to the now-defunct RaidForums cybercrime platform has... Read more »
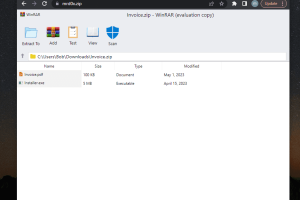
“file archiver in the browser” is a new phishing technique that can be exploited by phishers when victims visit a .ZIP domain. A new phishing technique called “file archiver... Read more »
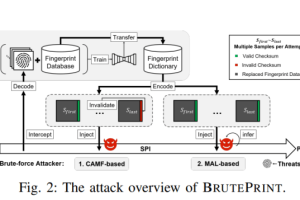
Researchers devised an attack technique, dubbed BrutePrint Attack, that allows brute-forcing fingerprints on smartphones to bypass authentication. Researchers have devised an attack technique, dubbed BrutePrint, that allows to brute-force... Read more »

