ESET researchers explained that enterprise network equipment that was discarded, but not destroyed, could reveal corporate secrets.
ESET researchers purchased a few used routers to set up a test environment and made a shocking discovery, in many cases, previously used configurations had not been wiped.
The experts pointed out that the data they found on the devices could be used to identify the prior owners, this information can be used by threat actors to breach their networks.
“Results reported here show that a majority of the secondary market core routers sampled contained recoverable configuration data from their previous deployments, replete with sensitive, and even confidential, data. This allowed ESET researchers to identify devices previously used in a data center/ cloud computing business (specifically, a router provisioning a university’s virtualized assets), a nationwide US law firm, manufacturing and tech companies, a creative firm, and a major Silicon Valleybased software developer, among others.” reads the report published by ESET.
The experts highlight the importance of adopting a procedure to correctly dismiss enterprise network equipment, like routers, due to the huge quantity of information they contain.
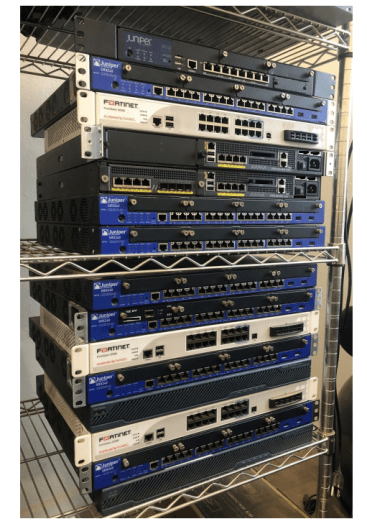
The ESET research team decided to conduct a more extensive test and purchased 18 used routers to determine which kind of information was possible to find on the dismissed network equipment and how threat actors can use them in future attacks against the company that discarded them.
This enterprise network equipment is widely adopted by organizations worldwide, ESET explained that they are a class of device that is commonly available at bargain basement prices in the secondary market
(US$50–150).
Below is the list of devices bought by ESET:
- 4 Cisco Systems ASA 5500 series
- 3 Fortinet FortiGate series
- 11 Juniper Networks SRX Series Services Gateway
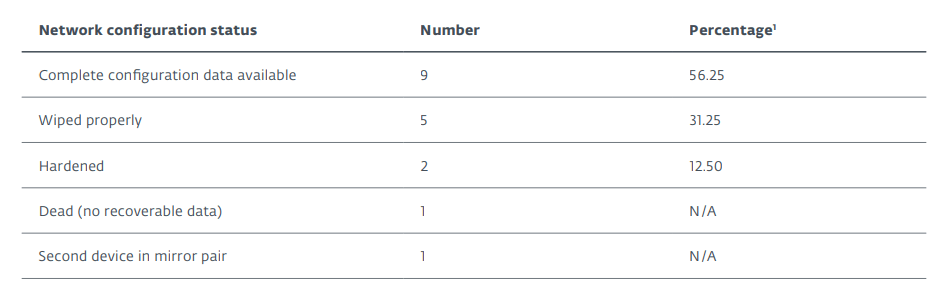
One of the routers was dead on arrival and two were a mirrored pair. The report state that the experts haven’t used procedures or tools of a primarily forensic or data recovery nature, nor were any techniques that required opening the routers’ cases.
The experts discovered that 56,25% of the devices contained trivially accessible and sensitive corporate information such as:
- 22% contained customer data
- 33% exposed data allowing third-party connections to the network
- 44% had credentials for connecting to other networks as a trusted party
- 89% itemized connection details for specific applications
- 89% contained router-to-router authentication keys
- 100% contained one or more of IPsec or VPN credentials, or hashed root passwords
- 100% had sufficient data to reliably identify the former owner/operator
Only five devices were properly wiped by the organizations that dismissed them.
Exposed corporate data and sensitive data include the maps of sensitive applications hosted locally or in the cloud. Some examples include Microsoft Exchange, Salesforce, SharePoint, SQL, Spiceworks, VMware Horizon, and VoIP.
The knowledge of the applications used by the organizations can allow attackers to use exploits for known vulnerabilities to launch attacks against enterprises.
“With this level of detail, impersonating network or internal hosts would be far simpler for an attacker, especially since the devices often contain VPN credentials or other easily cracked authentication tokens.” concludes the report.
ESET attempted to notify the former owners of the routers they had purchased, in some cases, they were responsive, while in others cases they were incredibly difficult or impossible to reach.
Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections:
- The Teacher – Most Educational Blog
- The Entertainer – Most Entertaining Blog
- The Tech Whizz – Best Technical Blog
- Best Social Media Account to Follow (@securityaffairs)
Please nominate Security Affairs as your favorite blog.
Nominate here: https://docs.google.com/forms/d/e/1FAIpQLSfaFMkrMlrLhOBsRPKdv56Y4HgC88Bcji4V7OCxCm_OmyPoLw/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, enterprise network equipment)
The post Hackers can hack organizations using data found on their discarded enterprise network equipment appeared first on Security Affairs.