Microsoft has addressed a zero-day in the Windows Common Log File System (CLFS) actively exploited in ransomware attacks.
Microsoft has addressed a zero-day vulnerability, tracked as CVE-2023-28252, in the Windows Common Log File System (CLFS), which is actively exploited in ransomware attacks. Microsoft fixed the issue with the release of Patch Tuesday security updates for April 2023.
The issue is an unspecified vulnerability in the CLFS driver that allows for privilege escalation. A local attacker can exploit this vulnerability to gain SYSTEM privileges. The vulnerability is easy to exploit and could be triggered without user interaction.
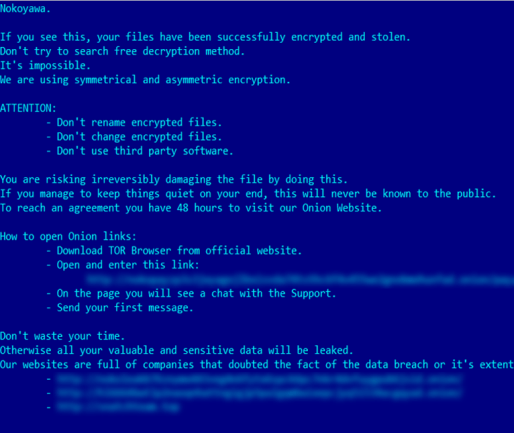
US CISA has added the flaw to its Known Exploited Vulnerabilities Catalog, based on evidence that threat actors are exploiting the flaw to escalate privileges and deploy Nokoyawa ransomware.
CISA orders federal agencies to fix this vulnerability by May 2nd, 2023.
Kaspersky Lab experts first reported that the CVE-2023-28252 flaw was exploited in attacks deploying the Nokoyawa ransomware.
On February 2023, Kaspersky experts observed a number of attempts to execute elevation-of-privilege exploits on Microsoft Windows servers belonging to small and medium-sized businesses in the Middle East, in North America, and previously in Asia regions.
The experts pointed out that while the majority of zero-days they have discovered in the past were used by APT groups, this zero-day was exploited by a sophisticated cybercrime group. This group is known to have used similar CLFS driver exploits in the past that were likely developed by the same author.
“The discovered exploit uses the vulnerability to corrupt another specially crafted base log file object in a way that a fake element of the base log file gets treated as a real one.” reads the analysis published by Kaspersky.
The experts will not share any additional details about the vulnerability and the exploit used by the threat actors to avoid other groups of attackers can use it.
“We see a significantly increasing level of sophistication among cybercriminal groups. We don’t often see APTs using zero-day exploits in their attacks, and now there are financially motivated cybercriminal groups that have the resources to acquire exploits for unknown vulnerabilities and routinely use them in attacks.” concludes the report. “Moreover, there are developers willing to help cybercriminal groups and to produce one exploit after another.”
Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections:
- The Teacher – Most Educational Blog
- The Entertainer – Most Entertaining Blog
- The Tech Whizz – Best Technical Blog
- Best Social Media Account to Follow (@securityaffairs)
Please nominate Security Affairs as your favorite blog.
Nominate here: https://docs.google.com/forms/d/e/1FAIpQLSfaFMkrMlrLhOBsRPKdv56Y4HgC88Bcji4V7OCxCm_OmyPoLw/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, zero-day)
The post Cybercrime group exploits Windows zero-day in ransomware attacks appeared first on Security Affairs.