Security researchers warn of hacking attempts in the wild exploiting critical vulnerabilities in VMware NSX Manager.
Cyber security firm Wallarm is warning of ongoing attacks exploiting the critical flaws, tracked as CVE-2021-39144 (CVSS score of 9.8) and CVE-2022-31678 (CVSS score of 9.1), in VMware NSX Manager.
VMware NSX is a network virtualization solution that is available in VMware vCenter Server.
The flaws can lead to remote code execution by pre-authenticated attackers. The CVE-2022-31678 flaw is an XML External Entity (XXE) vulnerability. An unauthenticated user may exploit this issue to cause a denial-of-service condition or unintended information disclosure.
The remote code execution vulnerability CVE-2021-39144 resides in the XStream open-source library. Unauthenticated attackers can exploit the vulnerability in low-complexity attacks without user interaction.
“Due to an unauthenticated endpoint that leverages XStream for input serialization in VMware Cloud Foundation (NSX-V), a malicious actor can get remote code execution in the context of ‘root’ on the appliance.” reads the advisory published by the company.
VMware warned of the existence of a public exploit targeting the CVE-2021-39144 vulnerability in October 2022, shortly after its disclosure.
The virtualization giant pointed out the impacted product had reached end-of-life (EOL) status in January 2022.
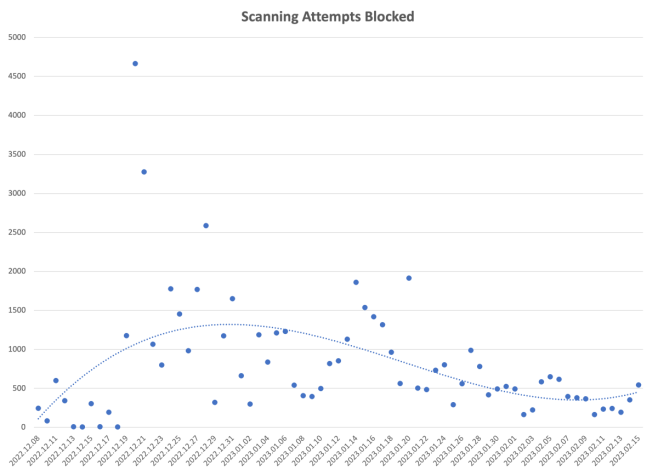
Wallarm Detect this week warned that, since December 2022, they are observing threat actors exploiting the issues. According to the experts, the CVE-2021-39144 vulnerability was exploited over 40 thousand times over the last 2 months.
“Active exploitation started on 2022-Dec-08 and keeps going.” reads the advisory published by Wallarm Detect. “Attackers are scanning from well-known data centers like Linode and Digital Ocean – over 90% of the attacks are coming from their IP addresses.”
“If successfully exploited, the impact of these vulnerabilities could be catastrophic, allowing attackers to execute arbitrary code, steal data, and/or take control of the network infrastructure.” continues the advisory.
Most of the attacks originated from Germany (33%), followed by the US (26%) and India (12%).
The peak in exploitation attempts was observed in late December, when the experts observed over 4,600 attacks per day. The number of exploitation attempts dropped in late January, to about 500 attempts per day.
“Companies can protect themselves from such vulnerabilities and exploits by keeping their software up-to-date. VMware has released updates for these vulnerabilities, but reports no other workarounds are available.” concludes the advisory.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, VMware)
The post VMware NSX Manager bugs actively exploited in the wild since December appeared first on Security Affairs.