Researchers dismantled a sophisticated ad fraud scheme, dubbed VASTFLUX, that targeted more than 11 million devices.
HUMAN’s Satori Threat Intelligence and Research Team dismantled a sophisticated ad fraud operation dubbed VASTFLUX.
The name VASTFLUX comes from the evasion technique “fast flux” and VAST, the Digital Video Ad Serving Template that was abused by threat actors in this fraudulent scheme.
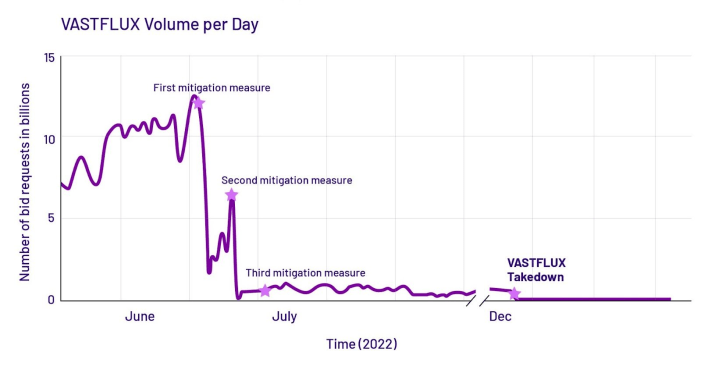
The researchers estimated that VASTFLUX accounted for more than 12 billion bid requests a day. The malvertising campaign spoofed more than 1,700 apps and 120 publishers, and targeted nearly 11 million devices.
According to the experts, the VASTFLUX operators have a deep understanding of the digital advertising ecosystem. The threat actors evaded ad verification tags to avoid detection.
“HUMAN’s Satori Threat Intelligence and Research Team uncovered and took down a sophisticated ad fraud operation we’ve dubbed VASTFLUX. This private takedown of an expansive and complex threat embodies the power of modern defense and collective protection.” reads the report published by HUMAN. “VASTFLUX was a malvertising attack that injected malicious JavaScript code into digital ad creatives, allowing the fraudsters to stack numerous invisible video ad players behind one another and register ad views.”
VASTFLUX exploited the restricted in-app environments that run ads, particularly on iOS, to place bids and display malicious ad banners.
Experts reported that several demand-side partners (DSPs) place a bid for the ad slot, in this case, when the bid was won by VASTFLUX, the purchasing/bidding ad server placed a static banner image in the slot and inject multiple malicious scripts.
“The injected scripts decrypt the ad configurations (the above screenshot). These configurations include a static banner image to put in the ad slot, a single video ad player hidden behind the banner image, and a series of additional parameters for more stacked video players.” continues the report. “The script then calls home to a command-and-control (C2) server for further information on what to place behind that static banner image.”
Then the injected scripts decrypt the ad configurations, which included a static banner image to display in the ad slot, a video ad player hidden behind the banner image, and a series of additional parameters for more stacked video players.
The script then communicates with a command-and-control (C2) server to retrieve further information on what to place behind that static banner image.
The received info includes a publisher ID and an app ID that is spoofed by VastFlux, geography and language settings, and a spoofed screen resolution.
VASTFLUX can stack as many as 25 ads on top of one another, allowing crooks to receive the payment for all of them, but not actually showing any to the user.
Below are the activities carried out by the security firm to dismantle the fraudulent scheme:
“The first cut VASTFLUX traffic dramatically, but resulted in the bad actors adapting. The second, only a few days after the first, reduced VASTFLUX traffic to fewer than a billion requests a day: a 92% reduction from the operation’s peak. The third, about two weeks after the first response, further impaired VASTFLUX activity.” Human concludes. “As of December 6th, bid requests associated with VastFlux, which reached a peak of 12 billion requests per day, are now at zero,”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
| [adrotate banner=”9″] | [adrotate banner=”12″] |
(SecurityAffairs – hacking, VASTFLUX)
[adrotate banner=”5″]
[adrotate banner=”13″]
The post Massive Ad fraud scheme VASTFLUX targeted over 11 million devices appeared first on Security Affairs.