Researchers warn that hundreds of Citrix servers have been hacked in an ongoing campaign exploiting the RCE CVE-2023-3519.
Security researchers from the non-profit organization Shadowserver Foundation reported that hundreds of Citrix Netscaler ADC and Gateway servers have already been compromised as part of an ongoing campaign exploiting the critical remote code execution (RCE) vulnerability CVE-2023-3519.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) recently warned of cyber attacks against Citrix NetScaler Application Delivery Controller (ADC) and Gateway devices exploiting the zero-day CVE-2023-3519. The Agency revealed that threat actors targeted a NetScaler ADC appliance deployed in the network of a critical infrastructure organization.
Citrix last week warned customers that the CVE-2023-3519 (CVSS score: 9.8) in NetScaler Application Delivery Controller (ADC) and Gateway is being actively exploited in the wild.
The vulnerability is a code injection that could result in unauthenticated remote code execution. The company added that successful exploitation requires that the appliance is configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) OR AAA virtual server.
“Exploits of CVE-2023-3519 on unmitigated appliances have been observed. Cloud Software Group strongly urges affected customers of NetScaler ADC and NetScaler Gateway to install the relevant updated versions as soon as possible.” reads the report published by Citrix.
The Citrix Cloud Software Group is strongly urging affected customers to install the relevant updated versions as soon as possible.
The U.S. CISA revealed that threat actors are exploiting the vulnerability to drop web shells on vulnerable systems.
“The Cybersecurity and Infrastructure Security Agency (CISA) released a Cybersecurity Advisory (CSA), Threat Actors Exploiting Citrix CVE-2023-3519 to Implant Webshells, to warn organizations about threat actors exploiting CVE-2023-3519, an unauthenticated remote code execution (RCE) vulnerability affecting NetScaler (formerly Citrix) Application Delivery Controller (ADC) and NetScaler Gateway.” reads the advisory published by CISA. “In June 2023, threat actors exploited this vulnerability as a zero-day to drop a webshell on a critical infrastructure organization’s NetScaler ADC appliance. The webshell enabled the actors to perform discovery on the victim’s active directory (AD) and collect and exfiltrate AD data. The actors attempted to move laterally to a domain controller but network-segmentation controls for the appliance blocked movement.”
CISA did not attribute the attack to a specific threat actor. The attackers exploited the flaw to deploy the the webshell that was used to perform discovery on the victim’s active directory (AD) and collect and exfiltrate AD data. The threat actors attempted to move laterally to a domain controller, but CISA pointed out that network-segmentation controls for the appliance blocked movement.
The attackers obtained encrypted passwords from NetScaler ADC configuration files, and the decryption key was stored on the ADC appliance.
Researchers from the non-profit organization Shadowserver Foundation this initially reported that at least 15,000 Citrix servers were exposed to CVE-2023-3519 attacks based on their version information. Most of the servers are located in the United States and Germany.
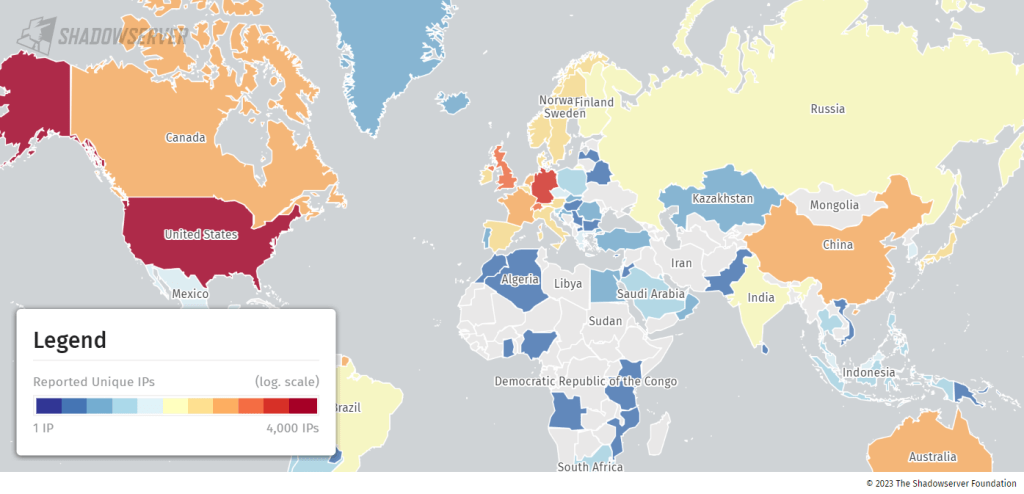
In an update provided by Shadowserver Foundation, the researchers from the non-profit organization confirmed that threat actors successfully installed webshells on at least 581 Citrix servers compromised by exploiting the above issue.
“We continue to report out daily lists of Citrix ADC/Gateway IPs that are known to be compromised with webshells installed (CVE-2023-3519 attacks). We see 581 instances on 2023-08-01.” states the organization.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Citrix)
The post Hackers already installed web shells on 581 Citrix servers in CVE-2023-3519 attacks appeared first on Security Affairs.

