Researchers observed threat actors spreading a trojanized Super Mario Bros game installer to deliver multiple malware.
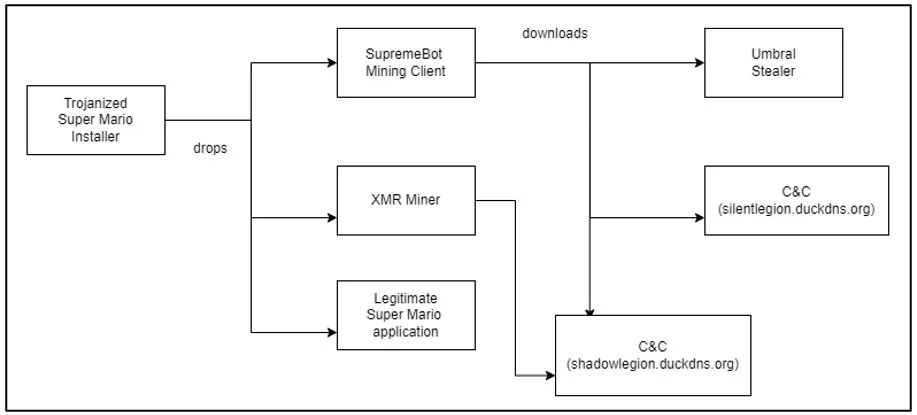
Researchers from Cyble Research and Intelligence Labs (CRIL) discovered a trojanized Super Mario Bros game installer for Windows that was used to deliver multiple malware, including an XMR miner, SupremeBot mining client, and the Open-source Umbral stealer.
The threat actors bundled a legitimate installer file of super-mario-forever-v702e with the malicious codes. The researchers pointed out that attackers target gamers because they often use powerful hardware for gaming, which is excellent for mining cryptocurrencies.
Mario Forever is a clone of the original Super Mario that attempts to recreate the classic Nintendo game very faithfully.
The threat actors tampered with the NSIS installer file “Super-Mario-Bros.exe,” the resulting executable file includes three separate executables: “super-mario-forever-v702e.exe,” which is the legitimate Super Mario game application, along with the malicious executables named “java.exe” and “atom.exe,” as shown below.
Upon executing the “Super-Mario-Bros.exe” file, it drops the “super-mario-forever-v702e.exe” executable in the %appdata% directory and executes it. While executing the file, an Installation Wizard is displayed to proceed with the installation of the “super-mario-forever-v7.02” program.
Once the software is successfully installed, a user interface is launched to play the Super Mario Forever game. However, an XMR (Monero) miner and a SupremeBot mining client are executed in the background.
“When “java.exe” is executed, the malware establishes a connection with a mining server “gulf[.]moneroocean[.]stream” to carry out cryptocurrency mining activities.” reads the report published by Cyble. “Concurrently, the malware gathers valuable data from the victim’s system, including computer name, username, GPU, CPU, and other relevant details. This sensitive information is then transferred to a Command and Control (C&C) server via the following URL API: “hxxp://shadowlegion[.]duckdns[.]org/nam/api/endpoint[.]php””
Upon executing SupremeBot (“atom.exe”), it creates a duplicate of itself and places the copy in a hidden folder in the installation directory of the game.
Then “atom.exe” initiates the execution of a scheduled task command that creates a new scheduled task entry that runs every 15 minutes without an end date.
Then the executable terminates the “atom.exe” process and removes its associated file from the system. Once deleted, the dropped file establishes a connection to the C&C server and sends it systems information, registers the client, and receives the configuration for the Monero miner.
In the last stage of the attack, the “atom.exe” retrieves an info-stealing executable, named “wime.exe”, from the C2. The executable unpacks itself and loads the open-source malware Umbral Stealer into the process memory.
The malware allows:
- Capturing screenshots
- Retrieving browser passwords and cookies
- Capturing webcam images
- Obtaining telegram session files and discord tokens
- Acquiring Roblox cookies and Minecraft session files
- Collecting files associated with cryptocurrency wallets.
“The expansive and interconnected user base within the gaming community serves as an appealing target for TAs aiming to exploit vulnerabilities and carry out various malicious activities.” concludes the report. “This coin-miner malware campaign leverages the Super Mario Forever game to target gamers and individuals utilizing high-performance computing machines for gaming purposes. Furthermore, the malware also deploys a stealer component to illicitly acquire sensitive information from the victims’ systems, aiming to generate additional financial profits. The combination of mining and stealing activities leads to financial losses, a substantial decline in the victim’s system performance, and the depletion of valuable system resources.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, gaming)
The post Trojanized Super Mario Bros game spreads malware appeared first on Security Affairs.

