Since March 2023, Unit 42 researchers have observed a variant of the Mirai botnet spreading by targeting tens of flaws in D-Link, Zyxel, and Netgear devices.
Since March 2023, researchers at Palo Alto Networks Unit 42 have observed a new variant of the Mirai botnet targeting multiple vulnerabilities in popular IoT devices. Below is the list of the targeted vulnerabilities:
| CVE/Product | Description |
| CVE-2019-12725 | Zeroshell Remote Command Execution Vulnerability |
| CVE-2019-17621 | D-Link DIR-859 Remote Command Injection Vulnerability |
| CVE-2019-20500 | D-Link DWL-2600AP Remote Command Execution Vulnerability |
| CVE-2021-25296 | Nagios XI Remote Command Injection Vulnerability |
| CVE-2021-46422 | Telesquare SDT-CW3B1 Router Command Injection Vulnerability |
| CVE-2022-27002 | Arris TR3300 Remote Command Injection Vulnerability |
| CVE-2022-29303 | SolarView Compact Command Injection Vulnerability |
| CVE-2022-30023 | Tenda HG9 Router Command Injection Vulnerability |
| CVE-2022-30525 | Zyxel Command Injection Vulnerability |
| CVE-2022-31499 | Nortek Linear eMerge Command Injection Vulnerability |
| CVE-2022-37061 | FLIR AX8 Unauthenticated OS Command Injection Vulnerability |
| CVE-2022-40005 | Intelbras WiFiber 120 AC inMesh Command Injection Vulnerability |
| CVE-2022-45699 | APsystems ECU-R Remote Command Execution Vulnerability |
| CVE-2023-1389 | TP-Link Archer Router Command Injection Vulnerability |
| CVE-2023-25280 | D-link DIR820LA1_FW105B03 Command injection vulnerability |
| CVE-2023-27240 | Tenda AX3 Command Injection Vulnerability |
| CCTV/DVR | CCTV/DVR Remote Code Execution |
| EnGenius EnShare | EnGenius EnShare Remote Code Execution Vulnerability |
| MVPower DVR | MVPower DVR Shell Unauthenticated Command Execution Vulnerability |
| Netgear DGN1000 | Netgear DGN1000 Remote Code Execution Vulnerability |
| Vacron NVR | Vacron NVR Remote Code Execution Vulnerability |
| MediaTek WiMAX | MediaTek WiMAX Remote Code Execution |
The botnet aims at taking control of D-Link, Arris, Zyxel, TP-Link, Tenda, Netgear, and MediaTek devices and uses them to carry out distributed denial-of-service (DDoS) attacks. The list of targeted devices includes routers, DVRs, access control systems, and Solar power generation monitoring systems.
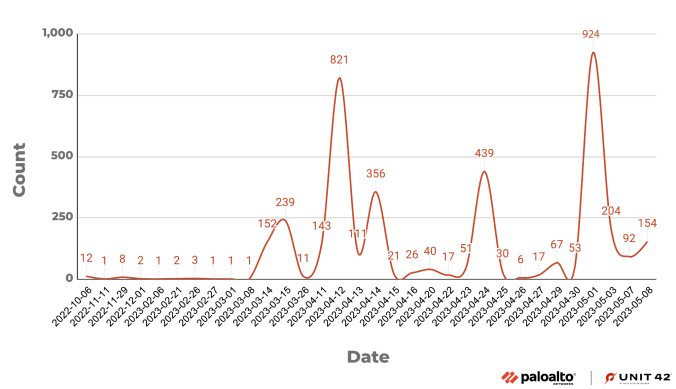
The researchers observed two campaigns, respectively in March and June.
Since the beginning of the attacks observed in October 2022, threat actors have enhanced the botnet by integrating exploits for new vulnerabilities.
The attack chain commences with the exploitation of one of the above issues, then the threat actor tries to download a shell script downloader from a remote server.
Upon executing the script, it would download and execute the proper bot clients for the specific Linux architectures:
- hxxp://185.225.74[.]251/armv4l
- hxxp://185.225.74[.]251/armv5l
- hxxp://185.225.74[.]251/armv6l
- hxxp://185.225.74[.]251/armv7l
- hxxp://185.225.74[.]251/mips
- hxxp://185.225.74[.]251/mipsel
- hxxp://185.225.74[.]251/sh4
- hxxp://185.225.74[.]251/x86_64
- hxxp://185.225.74[.]251/i686
- hxxp://185.225.74[.]251/i586
- hxxp://185.225.74[.]251/arc
- hxxp://185.225.74[.]251/m68k
- hxxp://185.225.74[.]251/sparc
Once executed the bot client, the shell script downloader will delete the client executable file to avoid detection.
“Based on behavior and patterns Unit 42 researchers observed while analyzing the downloaded botnet client samples, we believe the sample is a variant of the Mirai botnet.” reads the report published by Unit42. “Upon execution, the botnet client prints listening tun0 to the console. The malware also contains a function that ensures only one instance of this malware runs on the same device. If a botnet process already exists, the botnet client will terminate the current running process and start a new one.”
The researchers pointed out that the Mirai variant like IZ1H9 and V3G4 will first initialize an encrypted string table and then retrieve the strings through an index. However, this Mirai variant will directly access the encrypted strings in the .rodata section via an index
The approach allows the malware to remain under the radar and be faster.
This Mirai variant lack of brute forcing login credentials capability, which means that operators have to manually deploy it by exploiting the above vulnerabilities.
“The widespread adoption of IoT devices has become a ubiquitous trend. However, the persistent security concerns surrounding these devices cannot be ignored. The Mirai botnet, discovered back in 2016, is still active today. A significant part of the reason for its popularity among threat actors lies in the security flaws of IoT devices.” concludes the report. “These remote code execution vulnerabilities targeting IoT devices exhibit a combination of low complexity and high impact, making them an irresistible target for threat actors. As a result, protecting IoT devices against such threats becomes an urgent task.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, PoC exploit)
The post New Mirai botnet targets tens of flaws in popular IoT devices appeared first on Security Affairs.