The CheckMate ransomware operators have been targeting the Server Message Block (SMB) communication protocol used for file sharing to compromise their victims’ networks.
Unlike most ransom campaigns, CheckMate, discovered in 2022, has been quiet throughout its operations. To the best of our knowledge, it doesn’t operate a data leak site.
That’s quite unusual for a ransomware campaign since many prominent gangs brag about big targets and post them as victims on their data leak sites. They do this to raise the pressure for a victim to pay the ransom.
Cybernews research has recently detected new CheckMate activity. It turns out the gang has been actively targeting weakly-protected SMB shares.
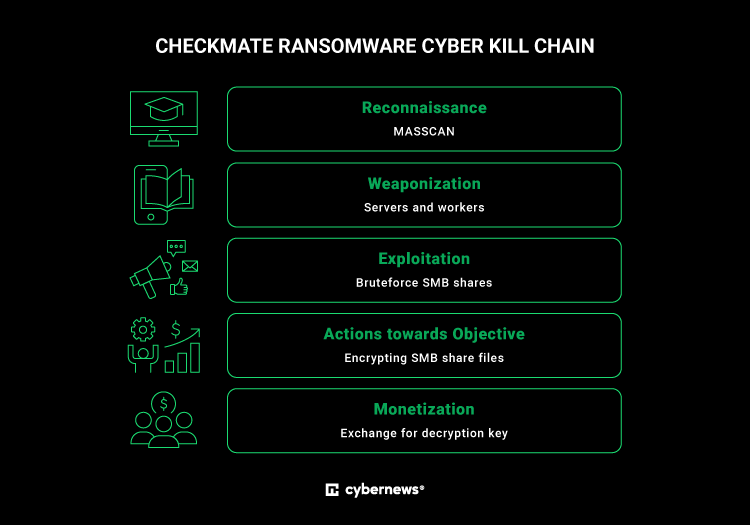
After gaining access to SMB shares, threat actors encrypt all files and leave a ransom note demanding payment in exchange for the decryption key.
Gang linked to Russia
The ransomware gang is known to be operating Kupidon, Mars, and CheckMate ransomware. All three types of malicious programs were discovered in 2021-22 and are believed to be of Russian origin.
According to Cybernews researchers, the impact of ransomware can be significant and wide-ranging. Risks to victims include:
- Financial loss
- Data loss
- Disruption of business operations
- Reputation damage
- Spread of malware
- Legal and regulatory consequences
While we don’t have enough information on the average ransom amount the gang demands from its victims, some publicly shared ransom notes indicate the group might be relatively modest. Typical amounts demanded are around $15,000 for the decryptor.
That’s a relatively small demand by usual standards. According to the recent report by the cybersecurity firm Coveware, average ransom payments during the last quarter of 2022 were over $400,000.
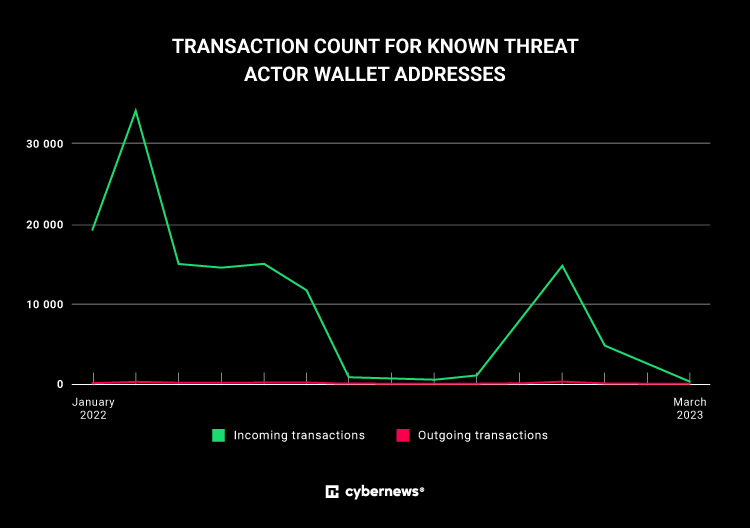
The Cybernews investigation identified crypto wallet addresses associated with the CheckMate operators and found thousands of incoming transactions in the first quarter of 2023. However, we can’t say with certainty that those transactions came from CheckMate’s victims.
Last year, QNAP, a network-attached storage (NAS) vendor, warned customers about the CheckMate ransomware activity going after internet-exposed SMB shares.
“Preliminary investigations indicate that Checkmate attacks via SMB services exposed to the internet and employs a dictionary attack to break accounts with weak passwords. Once the attacker successfully logs in to a device, they encrypt data in shared folders and leave a ransom note with the file name “!CHECKMATE_DECRYPTION_README” in each folder,” it said.
Why SMB?
SMB share, a network protocol originally developed by Barry A. Feigenbaum at IBM four decades ago, is used for file sharing and communication between computers on a local network. It works with different operating systems, including Windows, macOS, and Linux.
Generally speaking, connected users can access and browse files on shared folders as if they were on their local computers.
Given the protocol is quite commonly used to share resources and can be found on multiple devices across the network, they are an attractive target.
SMB shares often contain financial, personal, and intellectual data, among other valuable information. In this case, CheckMate operators abused the protocol to distribute ransomware.
Modus operandi
Threat actors start by scanning large networks at scale and speed to gather information and make up a list of potential targets. For that, they use an open-source tool called Masscan. As you’ve probably guessed from its name, it’s a high-speed scanner that can scan the entire internet in under five minutes, if we were to believe Github pundits.
Upon the discovery of weakly-protected SMB shares, attackers brute-force their credentials to gain access to the resources on a targeted network. Brute-force refers to trying out multiple username and password combinations with the hope of eventually guessing correctly. The attack is automated — attackers rely on specific software that can go through thousands, if not millions, of usernames and password combinations.
As per the Cybernews research team, threat actors successfully conduct 50-100 brute-force attacks on SMB shares, followed by file encryptions, per day.
Threat actors then use servers in different locations, mostly Russia, to store the files they need to run the ransomware campaign. Stored information often includes brute-forced SMB shares’ credentials and data on the victims’ databases.
For the encryption of the victims’ files, threat actors use Advanced Encryption Standard (AES) ciphers, a widely used symmetric encryption algorithm, which is commonly used to protect sensitive data.
The Cybernews research team observed threat actors using “AutoCryptor,” “Decryptor,” “ServerSmbWatcher,” and “SmbBruteManager” application files, as well as .php files and scripts to carry out the CheckMate ransomware campaign.
As is common with ransom gangs, CheckMate operators drop a text file on the victims’ desktops following the successful encryption of the target’s files.
In you are interested in mitigation give a look at the original post at
https://cybernews.com/security/checkmate-ransomware-victims/
About the author: Jurgita Lapienyt? at Chief Editor
We are in the final!
Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections where is reported Securityaffairs or my name Pierluigi Paganini
Please nominate Security Affairs as your favorite blog.
Nominate Pierluigi Paganini and Security Affairs here here: https://docs.google.com/forms/d/e/1FAIpQLSepvnj8b7QzMdLh7vWEDQDqohjBUsHyn3x3xRdYGCetwVy2DA/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ransomware)
The post Russia-affiliated CheckMate ransomware quietly targets popular file-sharing protocol appeared first on Security Affairs.

